What Is Mobile Threat Defense?
Why You Need Mobile Threat Defense
To some extent, mobile devices have always been targets for cybercriminals. A single smartphone may contain everything from personal photos and details to banking and healthcare information. And the more we rely on these devices, the more they become akin to pocket-sized treasure troves.
Every year, 42 million mobile malware attacks take place. For the most part, however, mobile security incidents have mainly involved individuals—until now.
Unfortunately, threat actors have shifted their focus from individuals to businesses and organizations.
The one constant in cybercrime is that threat actors invariably choose the path of least resistance when targeting potential victims. And with more people working from home and more organizations relaxing their mobile security policies, that path increasingly involves smartphones and tablets. Unfortunately, many of the smartphone features that make them so beneficial from a productivity standpoint also make mobile devices attractive targets for attackers:
- Less contextual data due to a simpler interface and smaller screen compared to desktops
- UI/UX design that emphasizes action rather than scrutinization
- A user environment that encourages splitting one’s attention, discouraging careful examination of permission requests or notifications
MDM, Mobile Application Management (MAM), and UEM tools only provide a partial answer to this problem. Standalone solutions cannot typically detect or respond to attacks specifically targeting Android and iOS devices. MTD addresses this.
It can also play a part in enabling Zero Trust Network Access (ZTNA), Extended Detection and Response (XDR), and Unified Endpoint Security (UES).
Mobile Threat Defense Benefits
The benefits of adopting MTD include:
- Easier adoption of bring-your-own-device (BYOD) policies.
- Monitoring of mobile threats at the device, network, and application layers without adding SecOps overhead.
- Protection of and visibility into an organization’s entire mobile fleet.
- Mitigation of common threats such as phishing attacks.
Additional MTD Benefits
- Ease of regulatory compliance for mobile devices
- Identification of both security vulnerabilities and potentially malicious activities by monitoring everything from OS updates to system parameters and device configuration
- Integration with MDM/UEM/MAM solutions that enables threat alerts and remediation based on existing policies
How Mobile Threat Defense Works
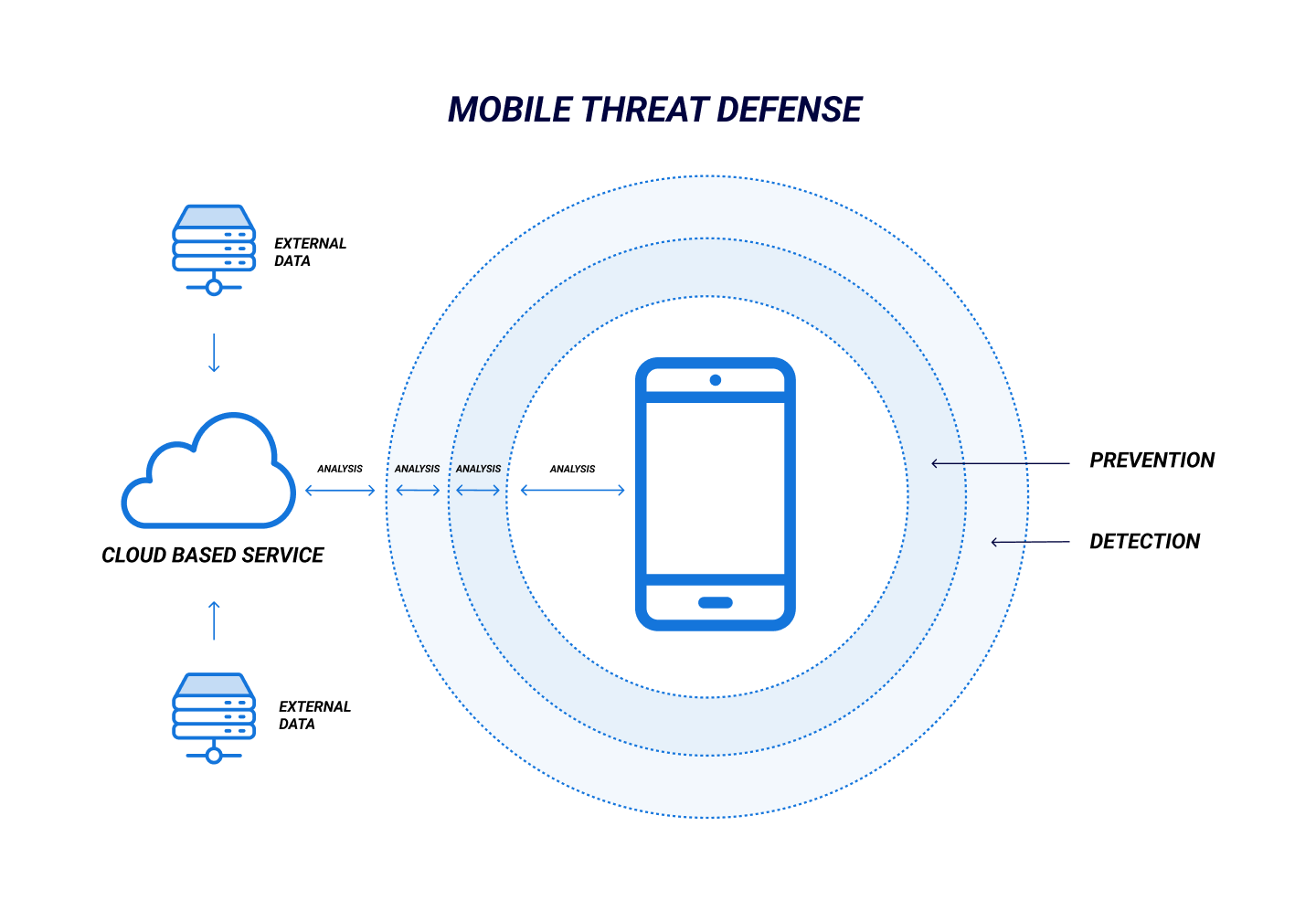
Per Gartner, because mobile malware must circumvent or otherwise disable built-in device controls, MTD focuses on identifying indicators of compromise and flagging abnormal behavior. This is typically achieved by combining data collected from supported devices with external threat intelligence. The orchestrated data is analyzed on premises, in the cloud, or on the device itself.
An MTD tool can detect configuration and application vulnerabilities and malicious apps and network attacks. When paired with User and Entity Behavior Analytics (UEBA), MTD can even be extended to identify unsafe or unusual end-user actions. Most MTD products support Android and iOS, and integrate readily with other mobile security solutions.
Gartner identifies four key deployment options for MTD:
- UEM Integrated. MTD enrollment and deployment are facilitated through a UEM solution, which also manages remediation.
- Standalone (On-Device). An MTD client is deployed on unmanaged or unenrolled devices.
- Standalone(Proxy-Based). The MTD client is typically deployed on-premises, diverting all network traffic through an analysis engine to be assessed for indicators of compromise.
- SDK/Embedded. MTD protects the application rather than the device on which it is installed, scanning for any activities which may render the application unsafe.
Mobile Threat Defense Best Practices
Remember that MTD is a means of improving one’s security hygiene and shoring up existing mobile device security—which means that an organization must have a strong baseline understanding of how devices are used, deployed, and protected before adoption.
Typically, this is achieved through a UEM or Enterprise Mobility Management (EMM) solution. An organization should also have a concrete deployment model and policies regarding passwords, authentication, acceptable use, jailbreaking, and sideloading. Patching and vulnerability management is also a must, and a governance, risk, and compliance (GRC) program is highly recommended.
It’s also essential that the organization’s leaders consider their industry, security requirements, and the sensitivity of the data typically accessed by and managed on mobile devices.
Once this groundwork has been established, MTD should be adopted—not in isolation, but as part of an overall security strategy. Integration with existing security solutions is imperative. Finally, an application-based deployment is typically the best option, particularly if a business plans to adopt ZTNA or XDR.
MTD vs MDM
MDM provides a business with a means of defining, applying, and enforcing security policies on mobile devices. The protection it offers against threats is mainly passive. A typical MDM tool cannot, for example, detect the presence of a malicious app on a user’s device.
On the other hand, MTD does not provide policy enforcement or policy management. Instead, it actively detects threats and diagnoses vulnerabilities. MTD typically includes remediation functionality, as well.
MDM and MTD are not opposing solutions but, rather, work best if deployed alongside one another.
FAQ
What is Mobile Threat Defense?
MTD refers to an emerging class of security solutions designed to protect Android and iOS against advanced threats. MTD goes beyond traditional EMM, MDM, and MAM, offering an extra layer of security by detecting, preventing, and remediating threats targeting a business’s mobile fleet and applications.
What features should you expect to see in a mobile threat defense solution?
MTD solutions typically encompass the following functionality:
Device-Level Detection
- OS version and security updates
- Device configuration
- Firmware
- System libraries
- System parameters
Application-Level Scanning
- Grayware detection
- Heuristics/signature-based malware scanning
- Code emulation/simulation
- Sandboxing
- Static/dynamic application security scanning
- Reverse engineering
Network-Level Monitoring
- Analyze traffic for potentially malicious and unsafe behavior
- Identify invalid certificates
- Detect stripping of TLS and “bidding down” attacks
- Flag malicious URLs
Additional MTD functionality may include:
- Vulnerability management
- App vetting
- Mobile-specific phishing protection
- OS-level attack prevention
- Risk management
- Content filtering
- Secure transport enforcement
- Cellular network attack prevention (i.e., SS7 vulnerabilities)
What are some of the security risks associated with mobile devices?
Mobile devices face many security risks, many of which are exacerbated by UI and UX. Phishing via email and SMS is a prevalent problem and an alarming number of mobile apps on both Android and iOS either leak data or contain multiple security vulnerabilities. Public or unsecured Wi-Fi networks are another issue, as is device theft.
What’s the difference between MTD and MDM?
MDM and MTD are complementary to one another. The former defines, applies, and enforces security policies, while the latter detects, identifies, and mitigates threats.
Why should a business deploy MTD?
Existing mobile security tools provide inadequate protection against businesses' mobile threats. Smartphones and tablets are also increasingly attractive targets for criminals seeking to compromise businesses. MTD solutions can protect an organization’s data and networks from mobile-based cyberattacks.
Like any other endpoint, a mobile device can be used as a springboard to give an attacker unrestricted access to your organization’s data and network. While crucial to a security posture, policy-based MDM solutions are insufficient protection. If your organization is to protect its people and assets, you need something more.
CylancePROTECT® Mobile leverages Cylance AI to provide your organization with everything required to keep your devices safe—blocking malware infections, preventing phishing attacks, and providing integrity checking. It allows you to secure your mobile workforce no matter where they are—without impairing their ability to do their jobs.