What Is Conti Ransomware?
Conti ransomware is one of the most prolific malware strains in the global cyber threat landscape. Conti has cost organizations more than $150 million in ransom fees since 2020 and has affected more than 1,000 businesses worldwide.
Conti is a second-stage malware attributed to the Wizard Spider group. It is believed to be the successor to the prolific Ryuk ransomware. While first-stage malware is purposed for gaining initial access, second-stage malware establishes command-and-control (C2) on a victim’s system, collecting information about the network and achieving primary strategic goals such as stealing and encrypting valuable data.
Attackers deploying Conti ransomware often employ a double extortion tactic, meaning that victims are coerced into paying ransom twice: once to regain access to their encrypted files and again to prevent stolen data from being released to the public.
Conti also uses a Ransomware-as-a-Service (RaaS) attack model. RaaS allows an affiliate to get paid for successfully deploying first-stage malware on an organization’s infrastructure, giving the primary threat actor immediate access to the target network for second-stage exploitation and coercion.
Latest Conti News
- Cerber Ransomware Operators Exploit Latest Atlassian Bug (bankinfosecurity.com)
- US and UK Sanction 11 TrickBot and Conti Cybercrime Gang Members (BleepingComputer)
- Conti's Legacy: What's Become of Ransomware's Most Wanted? (BankInfoSecurity)
- New LockBit Variant Targets macOS, Another Relies on Conti Source Code (SC Media)
- Both exfiltrates and encrypts victim’s data allowing a double extortion tactic
- Often deployed in Ransomware-as-a-service (RaaS) model attacks
- Uses process multithreading to spread and encrypt files quickly
Conti may be delivered using phishing, spear-phishing or vishing attacks, stolen remote desktop (RDP) credentials, or trojanized applications to gain initial remote access. Although Conti primarily targets Windows platform systems, more recent examinations of Conti malware toolkits have also discovered Linux exploits.
After initial access, malware connects to Conti’s command-and-control (C2) server and downloads the second-stage Conti C2 client and file encryption tools. Conti’s second-stage C2 malware employs a long list of penetration testing software tools such as Cobalt Strike beacon, PowerSploit, and AdFind to execute remotely and spread through a network to compromise high-value targets. Conti can also spread within a network via Server Message Block (SMB) and uses SMB exploitation as a strategy for encrypting data on other endpoints within the same network domain.
Like other ransomware, Conti attempts to disable existing security products that it detects and seeks to protect the contents of its malicious payloads by scanning the environment to determine if it is a sandbox environment used for malware analysis. Once the attacker has identified and compromised high-value targets, Conti exfiltrates valuable corporate data to an attacker-controlled server and then uses multi-threaded encryption to encrypt files quickly.
Conti attacks are often deployed in blitz attacks in which multiple organizations are compromised in a short period. A recent blitz example dubbed ARMattack (short for “armada”) saw Conti hack more than 40 companies within the span of about a month. Blitz attacks maximize the utility of novel and advanced malware techniques before the cybersecurity community has enough time to develop and share defensive measures.
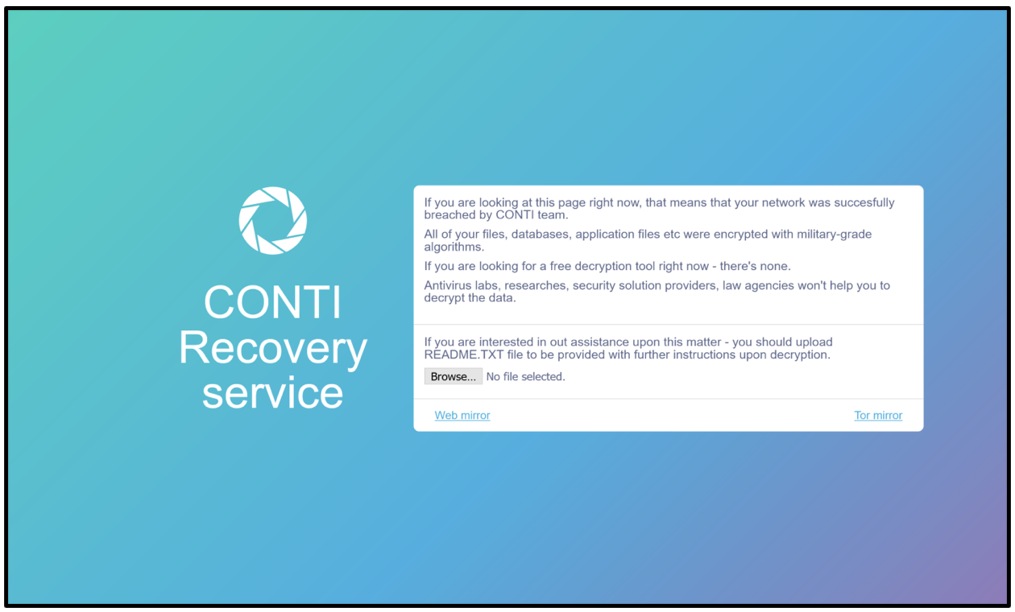
From the attack perspective, Conti typically targets personal documents, images, and videos—docx, xlsx, pdf, and mp4 files—and backup files. During the encryption process, files are encrypted with an AES-256 encryption key, then an RSA-4096 public encryption key and appended with a conti or CONTI extension. The malware also creates a text file in every folder containing the ransom message and instructions on how to contact the attackers and submit payment.
How to Protect Against Conti Ransomware
Defensive tactics that effectively prevent a successful Conti ransomware attack are similar to tactics used to prevent other malware, such as:
- Utilizing user-awareness training to reduce security incidents from phishing-based attacks
- Developing hardened authentication architecture and security to prevent malware’s ability to access sensitive resources
- Installing advanced endpoint detection and response products to enable timely identification and remediation of systems in the event of a breach