What Is LockBit Ransomware?
LockBit ransomware has been implicated in more cyberattacks this year than any other ransomware, making it the most active ransomware in the world. And while the average ransomware payment is nearly $1 million per incident, LockBit victims pay an average ransom of approximately $85,000—indicating that LockBit targets small-to-medium-sized organizations.
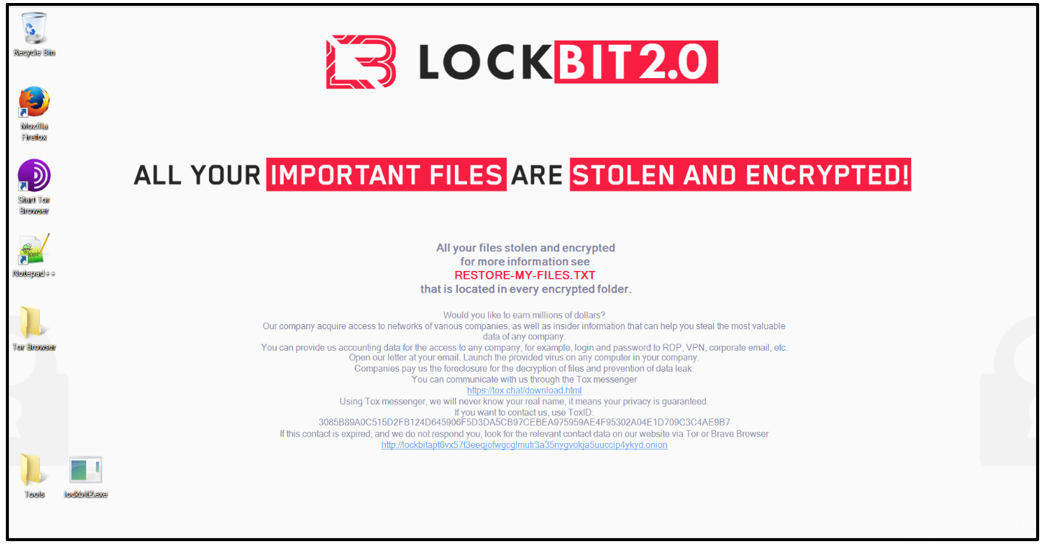
LockBit was first observed in September 2019. Since then, it has evolved: LockBit 2.0 appeared in 2021; LockBit 3.0, the current version, was discovered in June 2022.
LockBit seeks initial access to target networks primarily through purchased access, unpatched vulnerabilities, insider access, and zero-day exploits. “Second-stage” LockBit establishes control of a victim's system, collects network information, and achieves primary goals such as stealing and encrypting data.
LockBit attacks typically employ a double extortion tactic to encourage victims to pay, first, to regain access to their encrypted files and then to pay again to prevent their stolen data from being posted publicly. When used as a Ransomware-as-a-Service (RaaS), an Initial Access Broker (IAB) deploys first-stage malware or otherwise gains access within a target organization’s infrastructure. They then sell that access to the primary LockBit operator for second-stage exploitation.
Latest LockBit News
- Hackers Disrupt One of World’s Biggest Bank’s Trades with U.S. Treasury (CBC News)
- Russian Ransomware Lockbit Threatens to Leak Internal Data from The Weather Network on Dark Web (The Globe And Mail)
- LockBit Shuts Down Seaport in Japan: OT Attacks Have a Huge Impact (Techzine)
- Ransomware Attack on US Dental Insurance Giant Exposes Data of 9 Million Patients (TechCrunch)
Who Is the LockBit Gang?
The LockBit gang considers itself the “Robin Hood” of ransomware groups. While the FBI has not directly implicated the LockBit group as Russian, an assessment of LockBit’s public communications—which espouse a broadly anti-Western political view—indicates they have Russian origins with global affiliates. The group promotes the so-called “ethical” use of ransomware and claims they won’t target healthcare, education, charitable, or social service organizations.
The LockBit gang maintains a dark web portal on The Onion Router (TOR) network where they recruit talent and release the data of victims who refuse to meet their demands. The LockBit group assures victims that those who pay their ransom will have their data returned; establishing this is part of their business model.
LockBit 2.0 seeks initial access to target networks primarily through purchased access, unpatched vulnerabilities, insider access, and zero-day exploits. In LockBit’s RaaS model, the primary operating group recruits Initial Access Brokers (IAB) through advertisements on the dark web to obtain stolen credentials for Remote Desktop Protocol (RDP) or Virtual Private Network (VPN) access. The LockBit group also develops exploits for known software vulnerabilities to take advantage of unpatched or misconfigured enterprise networks.
After initial access is gained, LockBit 2.0 malware downloads C2 tools appropriate for the target environment. LockBit 2.0’s second-stage C2 malware uses standard penetration testing tools such as Cobalt Strike Beacon, MetaSploit, and Mimikatz, as well as custom exploit code. Like Conti, LockBit 2.0 can spread within a target network using worm-like functionality. LockBit 2.0 malware source code is also notorious for protecting itself from analysis by security researchers; tools are encrypted by default and only decrypted when a suitable environment has been detected.
LockBit 2.0 Targets
LockBit 2.0 primarily targets Windows systems, although some newer variations have been modified to attack Linux-based data center virtualization environments, including VMWare ESXi virtual machines. The malware is designed to attack victims in the United States, Canada, Europe, Asia, and Latin America. LockBit 2.0 ignores systems in the Commonwealth of Independent States and most Eastern Europe nations, with the notable exception of Ukraine.
LockBit typically targets mid-sized organizations. This may be due to LockBit’s unique RaaS model, which makes it easy for a disgruntled insider to act as an IAB, set their price, and collect ransom directly.
LockBit 2.0 IABs deploy an application known as “Stealbit” to attack a victim’s files with a customizable set of target file extensions. After targeted files have been copied to an attacker-controlled server, LockBit 2.0 installs itself in the Windows Registry as an automated boot process to maintain persistence so that it will auto-start when the computer is rebooted. LockBit 2.0 also tries to move laterally through a network via connections to other hosts to deploy the ransomware on other machines.
Then the malware installs a custom icon file and proceeds with multi-threaded encryption using a pair of ECC (Curve25519) session keys, with the private key encrypted with an ECC public key stored in the Windows Registry. Earlier versions of LockBit appended a “.acbd” file extension to differentiate ransomed files; newer versions use a “.lockbit” extension. Finally, LockBit changes the desktop wallpaper to the signature LockBit ransom warning image and a ransom note titled “Restore-My-Files.txt” is dropped in each affected directory.
How to Protect Against LockBit Ransomware
Preventing a successful LockBit 2.0 attack requires effective cybersecurity and maintaining an effective backup strategy that includes encrypted offline and offsite backups.
To mitigate the risk of a LockBit breach, implement robust access controls with strong password policies and multi-factor authentication, maintain a vulnerability management program that ensures security updates are applied when they are released, and architect internal networks with critical resources segmented. Additionally, enable “Protected Files” in the Windows Operating System to ensure that LockBit cannot alter critical system files.