XDR and EDR Features
Rapid Threat Response
Preventative Approach
Threat Hunting Support
What Is the Difference Between XDR and EDR?
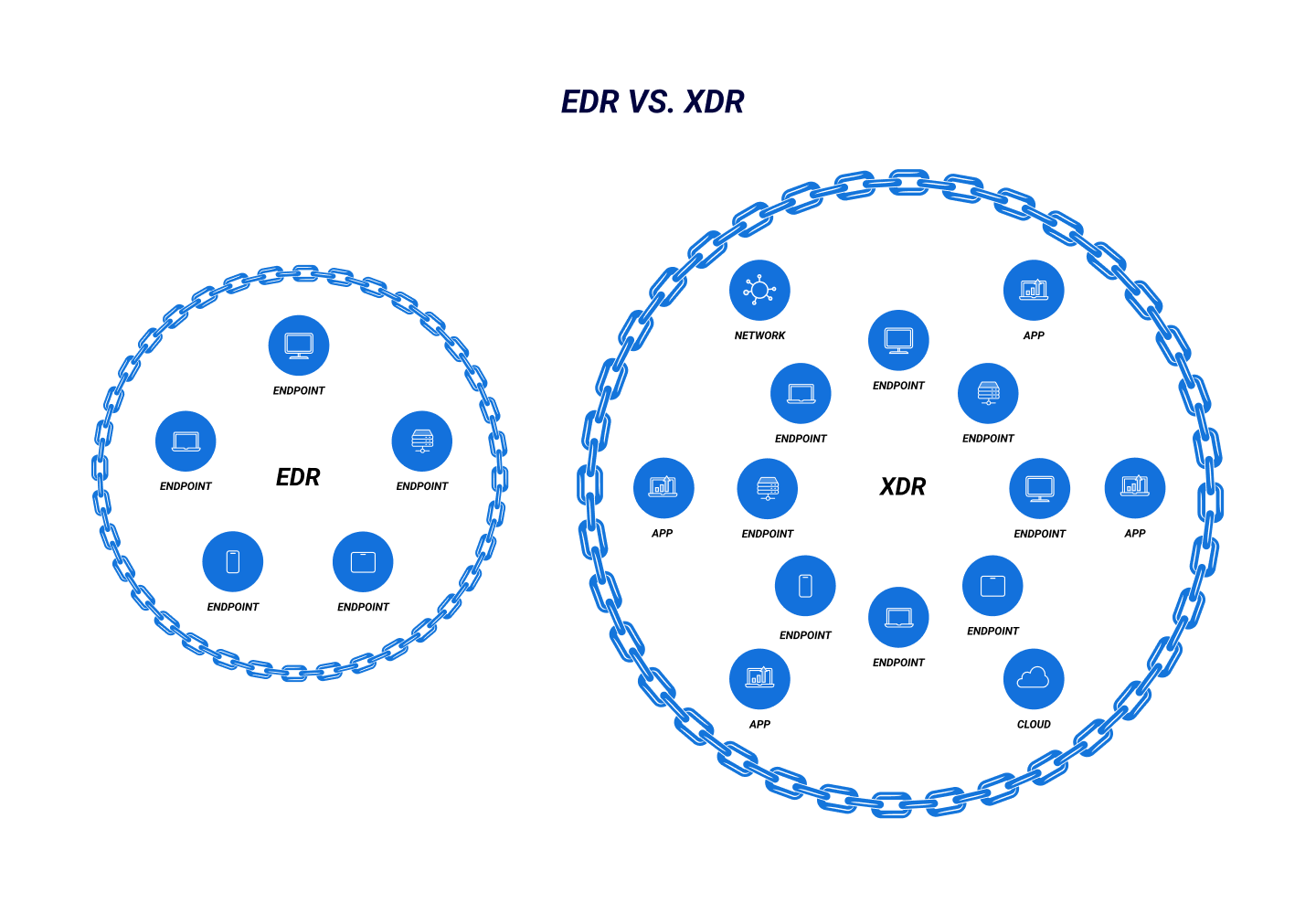
Both EDR and XDR involve continuous monitoring, threat detection, and automated response to cyber threats, but EDR's scope is limited to endpoints while XDR is more comprehensive. By unifying the detection and analysis of cyber threats against an organization's network, cloud workspaces, and endpoints, XDR can more effectively ward off cyberattacks than EDR alone.
The initial purpose of an EDR system was to provide perimeter-wide protection for an enterprise network. EDR products monitor events of endpoint agents and collect telemetry data for contextual information to detect suspicious activity and remediate issues. EDR functionalities provide proactive endpoint security to help security teams address gaps and blind spots. However, EDR systems can't save the network or system independently. In addition, they offer limited visibility into the actions of threat actors at the endpoints.
On the other hand, XDR takes a broader view of data integration from an endpoint, cloud, identity, and different digital environments. As a result, it fills the information gaps and, unlike EDR, brings clarity into every phase of an attack, starting from endpoint to payload.
What's Better: XDR or EDR?
When deciding between XDR and EDR, organization leaders should consider their computing environment, its architecture, and the type of security controls needed to protect critical assets. Additionally, the integration of XDR into an organization's security platform can enable it to collate system-wide information, providing a more accurate idea of previous attacks—and those in progress.
While EDR has limitations, XDR offers complete protection to the network and systems with increased network distribution, incorporation of external services, and broader system access.